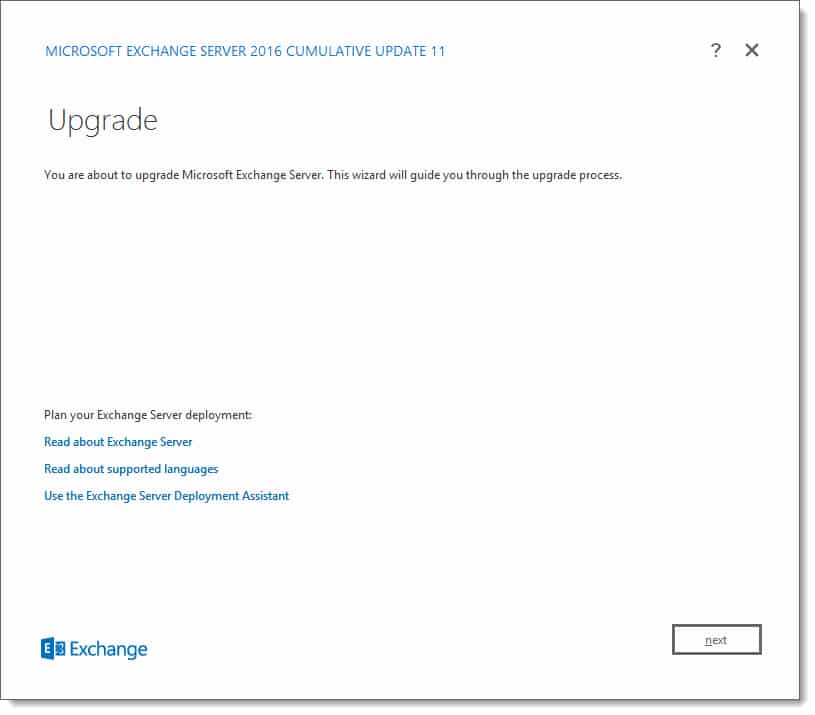
Last week was a big week for Exchange 2016. Microsoft released Cumulative Update 11. At this time no updates were released for Exchange 2013 or Exchange 2010. Exchange 2013 entered extended support back on April 10th, and Microsoft announced in June that cumulative update 21 was the last planned update for Exchange 2013.
As always, test these updates in a lab first! I recommend checking out this 7-part guide on configuring Exchange in your lab. It doesn’t take much to get one going.
The updates are as follows:

Exchange 2016 Cumulative Update 11 | KB4134118 | UM Language Pack

Exchange 2010 SP3 Rollup 24 | KB4458321 (released September)

Exchange 2010 SP3 Rollup 23 | KB4340733 (released August)
So, what’s new in these Cumulative Updates?
Cumulative Update 11 now officially supports .NET Framework 4.7.2. Framework 4.7.2 is only optional at this point and will not become mandatory until the June 2019 updates. Due to no quarterly update scheduled for December, it is expected that CU13 will be the first version to enforce 4.7.2 as a requirement.
Support for 4.7.2 has been officially added to Exchange 2013 CU21, which was released back in June. 4.7.2 will also be a requirement for Exchange 2019. However, 4.7.2 is preinstalled with Windows Server 2019, so it will not require a separate download. For a great resource on navigating which .NET update goes with which CU I recommend reading Upgrade Paths for CU’s & .NET by Michel de Rooij.
In the June updates, it was stated that all Exchange roles would require Visual C++ 2013. Microsoft has since clarified this statement to the following:
- Mailbox role will require both Visual C++ 2012 & Visual C++ 2013
- Edge & Management tools only require Visual C++ 2012
Cumulative Update 11 will now perform prerequisite checks to confirm the necessary versions of Visual C++ are installed.
These updates contain 22 security and bug fixes. Check KB 4134118 for a list of issues CU11 resolves.
Upgrade considerations
As a reminder, the September 2017 cumulative update introduced a forest functional requirement of Server 2008 R2. This means that if you are upgrading from CU6 or earlier all domain controllers in the forest must be running Server 2008 R2 and higher.
Exchange 2016 Cumulative Update 11 does not include schema updates. If upgrading from CU 7-10 then there are no schema changes. However, if migrating from CU 6 or earlier you will need to perform a schema update.
To learn how to extend and verify the schema check this guide. For a quick reference on schema and build numbers check here.
In addition to the schema, you will want to run SETUP /PrepareAD to get the latest RBAC definitions. The graphical setup performs this step automatically assuming you have permissions.
More Awesome News
It’s amazing to believe that Microsoft Ignite was almost a month ago. With 1,610 sessions Microsoft gave us a massive amount of announcements and demonstrations of new product features. If not already, I highly recommend checking out the article 15 Ignite sessions every Exchange admin should see (2018 edition). In this article, there are extensive notes on what each session contained. In addition, those notes contain timers so you can jump to the section that interests you the most. Hopefully, it will also serve as a reference if you need to search for a certain announcement or feature weeks (or even months) later.
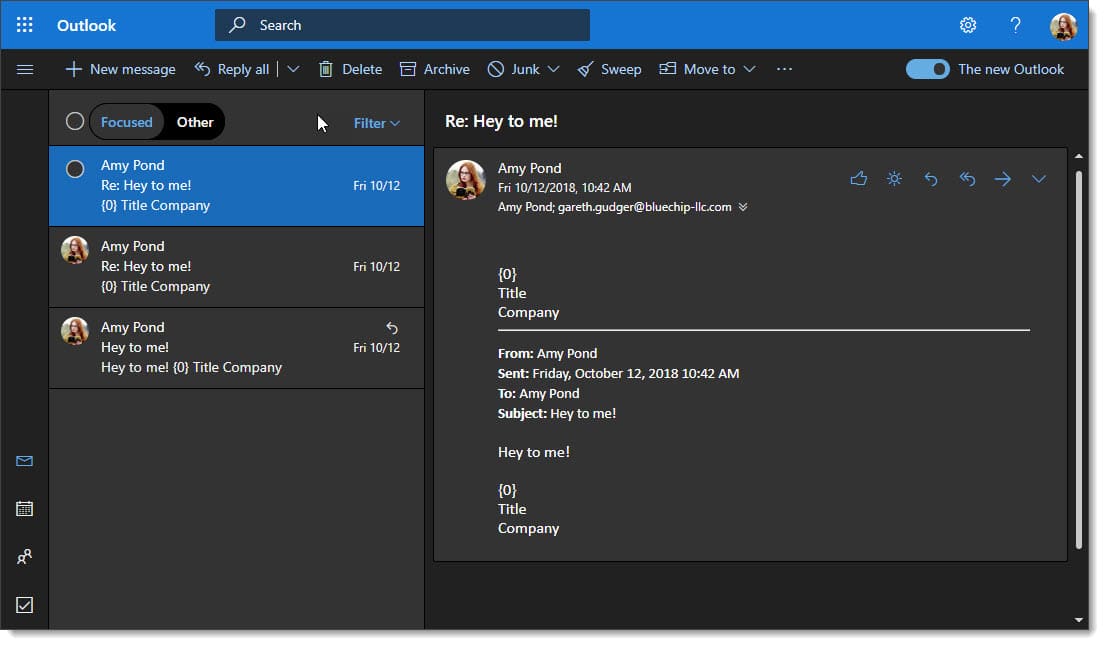
My favorite announcement, aside from Exchange 2019, was the announcement of dark mode coming to various Outlook clients. I recommend checking out the article on enabling dark mode in Outlook on the Web.
As a reminder, Microsoft will be ending support for TLS 1.0 and 1.1 protocols in Office 365 on October 31st, 2018. While Microsoft will not block these older protocols they do intend to deprecate these older protocols in the future. I highly recommend acting on the information in the following articles before the 31st so you can remain in a supported state.
- Exchange Server TLS guidance: Getting Ready for TLS 1.2 – Part one acts as both an introduction and lists the minimum updates needed by both Exchange and Windows Server. At a minimum, it is important to get your environment to this level.
- Exchange Server TLS guidance: Enabling TLS 1.2 and Identifying Clients Not Using It – Part two provides guidance on how to enable TLS 1.2. It provides guidance on various protocols, such as HTTPS, SMTP, POP & IMAP. Last, it provides instructions on how to validate the version of the TLS protocol in use.
- Exchange Server TLS guidance: Turning Off TLS 1.0/1.1 – Part three identifies how to use the registry to disable TLS 1.0 and 1.1.
Earlier in the month, Microsoft announced a feature to control connections to public folders. Through the use of Set-CASMailbox & Set-OrganizationConfig, an administrator can define whether a user will receive connection details to the public folder infrastructure in their Autodiscover response. This allows an organization to restrict who can see public folders, which may be useful when sizing a public folder infrastructure, or, during acquisitions and divestitures. Microsoft is considering bringing this feature to on-premises Exchange.
Also in October Microsoft announced that it had a program designed to eliminate the need for basic authentication in Office 365. The idea is to promote the sole use of modern authentication across all connections to Office 365 and give administrators the necessary tools to make that change. The movement to eliminate basic authentication is in response to growing threats on the internet. You can read more about this program here (currently in public preview). Microsoft had previously announced plans to deprecate basic authentication to Exchange Web Services by October 13th, 2020.
During Ignite Microsoft announced several improvements coming to Organization Configuration Transfer in the hybrid configuration wizard. In the initial version, the Organization Configuration Transfer (OCT) would offer to perform a one-time migration of your retention, Outlook web app, mobile device, and ActiveSync policies. The new version offers to perform a one-time migration of several additional items including device access rules, address lists, policy tips, malware settings, data loss prevention policies, and various other organization-level settings. In addition to these extra policies, the administrator is also given the PowerShell commands to roll back all configuration performed by the OCT, and the ability to resolve conflicting policies.
Microsoft also announced the new Hybrid Agent, which allows an organization to perform mailbox moves and free/busy lookups with Office 365 without publishing your on-premises Exchange to the internet. Keep in mind the initial release of the Hybrid Agent does not address things like hybrid mail flow, which will still require inbound port 25. The Hybrid Agent is in private preview.
Back in July Microsoft announced that the hybrid configuration wizard would identify an unlicensed Exchange server and offer a hybrid key. Previously the hybrid edition key was acquired manually through a dedicated portal. Going forward the hybrid configuration wizard is the only method to obtaining the hybrid edition key.
For more information on the Organization Configuration Transfer, Hybrid Agent, and acquiring a hybrid key be sure to check out Jeff Kizner’s Ignite session. You can find notes and timers on this session in the article 15 Ignite sessions every Exchange admin should see (it’s the second session on the list).
We need your help – Universal Signatures
Earlier this year fellow MVP, Jeff Guillet, spearheaded an initiative for universal signatures. The outcome of this initiative was two-fold.
- When a user sets a signature on one device that signature should be synchronized across all devices (desktop, mobile, web app)
- A signature should be stored in the mailbox so it is not lost if a device is wiped or an Outlook profile is recreated
The support on Twitter and UserVoice has been overwhelming. At the time of writing, we have 6,283 votes and 770 comments on UserVoice. This puts our feature request at first place in the Outlook for Windows forum, beating second place by 4,525 votes.
But we still need your help. We need to keep this momentum going! If you think this is an awesome feature please vote for it on UserVoice. It only takes a few seconds. If you have already voted, please spread the word on all your social networks. Let’s get this request over 10,000 votes! Please vote here.
You can read more about Jeff’s initiative on his blog.

So what do you think is coming next? What would you like to see? Drop a comment below or join the conversation on Twitter @SuperTekBoy.

Leave a Reply