Last
As always, test these updates in a lab first! I recommend checking out this 7-part guide on configuring Exchange in your lab. It doesn’t take much to get one going.
The updates are as follows:

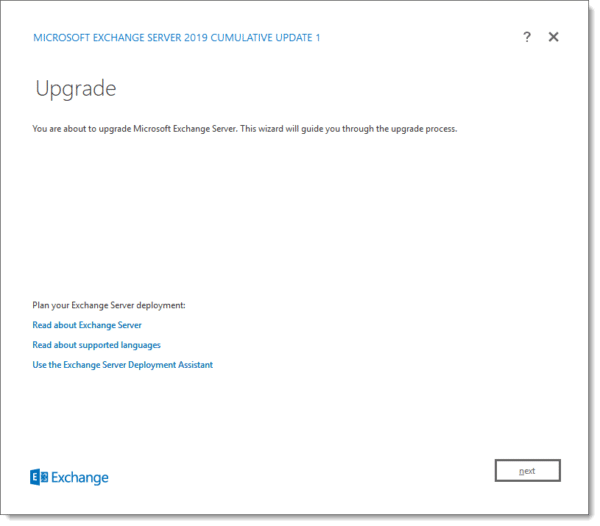
Exchange 2019 Cumulative Update 1 (VLSC)| KB4471391

Exchange 2016 Cumulative Update 12 | KB4471392 | UM Language Pack

Exchange 2013 Cumulative Update 22 | KB4345836 | UM Language Pack

Exchange 2010 SP3 Rollup 26 | KB4487052 (released February)

Exchange 2010 SP3 Rollup 25 | KB4468742 (released January)
Only 325 days left for Exchange 2010
Here is a quick reminder that extended support for Exchange 2010 is coming to an end. After January 14th, 2020, no further technical support or updates will be available. This includes security, bug, and time zone updates.
Unfortunately, there is no direct path to Exchange 2019 from 2010. If you do plan to stay on-prem you will need to migrate to either 2013 or 2016 (I’d recommend 2016 as 2013 is now in extended support). From there you can migrate to 2019. Alternatively, you can migrate to Office 365.
For more information about the Exchange 2010 life-cycle check out the Exchange Team blog.
So, what’s new in these Cumulative Updates?
Push notifications are one type of notification a developer can leverage in their application to add value. An example of a push notification might be the notification of new mail on a mobile device.
In this series of cumulative updates, the Exchange Team has changed the way it initiates push notifications through Exchange Web Services. This is in direct response to a security flaw where an attacker could intercept push notifications to gain access to credentials streamed via NTLM. These cumulative updates mitigate this attack by removing these credentials from the stream. Microsoft documents this resolution in KB4490060.
After applying this cumulative update, Microsoft recommends forcing the computer account to change its password by using either the Reset-ComputerMachinePassword cmdlet or, NETDOM. In addition, Microsoft recommends every organization review its user password expiration policies.
In further response to the security flaw, Microsoft is reducing the number of rights Exchange has in Active Directory when operating in a shared permission model.
In a shared permission model, Exchange administrators have the ability to create security principals in Active Directory and mail-enable those security principals. This includes the ability to create a new user as you are creating a mailbox, or, the ability to remove a user when you remove a mailbox. This also extends to tasks such as being able to create a distribution group, or, modify distribution group members.
In a split permission model, the Exchange administrator is restricted from these tasks and can only mail-enable, or, mail-disable existing objects (e.g. users, groups, or contacts) that were created by an administrator with Active Directory rights.
Going forward the shared permission model will have fewer Active Directory rights, but that does not mean reduced functionality for Exchange administrators.
If you are applying the latest cumulative updates in Exchange 2013, 2016, or, 2019, these changes are applied for you automatically. If you are running Exchange 2010, you must apply these changes manually. This process is detailed in KB4490059.
Note: No changes are being made to the split permissions model.
While these updates do not contain any changes to the schema, you will need to run SETUP /PrepareAD to apply these security changes. If you are running multiple versions of Exchange in coexistence, run SETUP /PrepareAD from the newest version of Exchange. For example, if you have Exchange 2013 and Exchange 2019, run SETUP /PrepareAD from Exchange 2019 CU1.
Despite these two big fixes each cumulative update contains a number of other fixes. Be sure to check out the knowledge base articles listed at the top of this article to review all fixes.
Upgrade considerations
Exchange 2019 Cumulative Update 1 does not include schema updates.
Exchange 2016 Cumulative Update 12 does not include schema updates. If upgrading from CU 7-11 then there are no schema changes. However, if migrating from CU 6 or earlier you will need to perform a schema update.
Exchange 2013 Cumulative Update 22 does not include any schema updates. If upgrading from CU 7-21 then there are no schema changes. However, if migrating from CU 6 or earlier you will need to perform a schema update.
Despite the lack of a schema update, you will need to run SETUP /PrepareAD to get the new security changes referenced in the previous section.
Note: In a multi-domain environment where the Exchange administrator may lack the necessary permissions in every domain, or, you operate a split permissions model, a domain admin will need to run either SETUP /PrepareDomain (in each domain), or, an Enterprise Admin will need to run SETUP /PrepareAllDomains.
Visual C++ 2013 Redistributable is a requirement for updating mailbox servers to Exchange 2013 CU22, Exchange 2016 CU12 & Exchange 2019 CU1. You will need to install this before running the setup. If this package is missing, setup will not continue. Edge Transport and the management tools require Visual C++ 2012 Redistributable.
More Awesome News
Hybrid Agent
Microsoft released the new Hybrid Agent into
For more information on the Hybrid Agent be sure to check out Jeff Kizner’s Ignite session. You can find notes and timers on this session in the article 15 Ignite sessions every Exchange admin should see (it’s the second session on the list).
Unified Messaging
In February 2020, Unified Messaging in Exchange Online will be retired. This follows the announcement of Unified Messaging being dropped from Exchange 2019 back in October. It also marks the end of Unified Messaging in the Exchange product line.
Customers leveraging Exchange Online Unified Messaging for either Skype for Business 2015 or Lync 2013 will be automatically transitioned to Cloud Voicemail. Microsoft announced this transition will be transparent to end users, begin in March 2019, and customers will receive transition notifications as early as February. Organizations on Lync 2010 will not be transitioned. Anyone on Lync 2010 will need to migrate to Skype for Business to use Cloud Voicemail.
Customers leveraging Exchange Online Auto-Attendant will need to manually transition attendants and phone numbers to Cloud Auto-Attendant before February 2020.
The main benefit of this change is that it folds all products–Skype for Business on-premises, Skype for Business online, and Teams–into the same voicemail and phone system. This allows Microsoft to focus all development and support onto a single product.
MetaCache Database Setup Guide
Last week Microsoft announced the general availability of the MetaCache Database (MCDB) setup guide. This setup guide includes a new PowerShell script, Manage-MetaCacheDatabase.ps1, for implementing and managing the MCDB. This script comes included with Exchange 2019 under the %ExchangeInstallPath%Scripts directory.
For a general overview of the MCDB, be sure to check out the Ignite 2018 session “Email search in a flash! Accelerating Exchange 2019 with SSDs”. The content on the MCDB starts around the 19-minute mark. You can find more notes and timers on that session here.
Public Folders
Microsoft had previously added support for migrating up to 250,000 legacy public folders to Exchange Online. In October Microsoft extended the 250,000 folder support to modern public folders. The previous limit was 100,000 modern public folders.
The Exchange Team also improved the speed and reliability around public folder migrations to Exchange Online. By rearchitecting how the cleanup tasks are performed large migrations, which could take as long as 3-4 days, now take 15-20 hours. Non-fatal errors (which aren’t related to data integrity) have been reclassified to mark the migration batch as successful versus a failure. These previous failures would result in admins having to retry the migration to get success.
A new cmdlet, Remove-PublicFolderMailboxMigrationRequest, was released. This new command allows an administrator to remove an individual public folder mailbox from a migration batch. This is particularly useful when a public folder mailbox has become duplicated or orphaned.
More in Awesome
The article Advanced Office 365 Routing: Locking Down Exchange On-Premises when MX points to Office 365 is a detailed guide on how another Office 365 tenant could purposely bypass your MX record and send it directly to your on-prem Exchange server. The article guides you through different configurations to block this behavior.
The Exchange Team has released an Exchange Online Fiddler extension. Fiddler is a free tool developed by Telerik which is used to intercept and diagnose web traffic (HTTP and HTTPS). The Exchange Online extension helps identify specific data in captures to make it easier for administrators to diagnose client connections to Exchange Online.
The Exchange Team has also added session identifiers to the Exchange Online audit logs. This allows administrators to better identify all activities that belong to a particular session. This session ID is preserved even if there is a token refresh, or, a hacker is launching their attack via multiple IP addresses. This will help distinguish activity by a hacker versus a legitimate user. It is worth noting that session ID only works with modern authentication and not basic authentication. Microsoft documents the process of disabling basic authentication in Exchange Online here.
In the article New Outlook for iOS and Android App Config Policy, Ross Smith announces how account configuration can be pushed to Outlook mobile using InTune. This does require the user’s device to be enrolled in InTune. While both basic authentication and modern authentication are supported, modern auth provides more control features to the admin, such as restricting Outlook mobile to only work accounts.
Need a refresher from Ignite 2018?
It’s amazing to believe that Microsoft Ignite was almost 5 months ago. With 1,610 sessions Microsoft gave us a massive amount of information. If you need a refresher on all the features and news announced at Ignite, I highly recommend checking out the article 15 Ignite sessions every Exchange admin should see (2018 edition). In this article, there are extensive notes on what each session contained. In addition, those notes contain timers if you need to jump to a specific topic.

So what do you think is coming next? What would you like to see? Drop a comment below or join the conversation on Twitter @SuperTekBoy.

It’s really annoying that you need a VLSC subscription to be able to download Exchange 2019 and the cumulative updates.
How do I install and test Exchange 2019 at home in a lab environment without having a volume subscription?
Hey Bob,
If you have access to an MSDN subscription you can also get access to Exchange 2019 and its cumulative updates for your lab that way. But I agree, it is rather frustrating.
I don’t have an MSDN subscription either so what is a learner/lab tester to do?
Thanks for this info. I knew .NET Framework was a REQ, but not the Visual C++ Redistributable pkg…. this is why my upgrade to CU12 failed during /PrepareAD. Appreciate the post!
Thank for this info, this exchange helped us a lot.