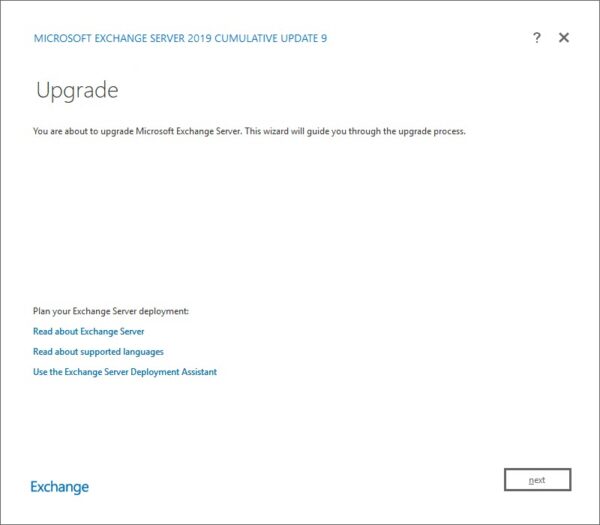
This week saw some critical cumulative updates for Exchange 2016 and Exchange 2019. These new updates contain the security patches previously released on March 2nd. Organizations that apply these cumulative updates don’t need to install the previous security patch.
The exception to this is those organizations on Exchange 2010 or Exchange 2013, where no update has superseded the March 2nd security patch. Those on Exchange 2010 and 2013 must ensure that they have the March 2nd patch applied as soon as possible.
The updates are as follows:

Exchange 2019 Cumulative Update 9 | KB4602570

Exchange 2016 Cumulative Update 20 | KB4602569 | UM Language Pack

Exchange 2013 Security Update | KB5000871 (March 2nd Security Patch)

Exchange 2010 SP3 Rollup 32 | KB5000978 (March 2nd Security Patch)
Tackling the March 2nd security exploits
It is imperative to protect yourself from the exploits published on March 2nd. HAFNIUM, a cyberespionage group with ties to the Chinese government, has leveraged these Exchange Server exploits to infiltrate victims’ networks to deliver malware and other malicious payloads with varying motives, primarily to exfiltrate confidential data.
First, patching is imperative.
- Those on Exchange 2016 or 2019 should apply the latest cumulative update.
- Those on Exchange 2013 will need to install Cumulative Update 23 (released June 2019), followed by the March 2nd, 2021 security patch.
- Those on Exchange 2010 need to install rollup 32.
Note: On March 8th Microsoft updated the security patch allowing it to be installed on older cumulative updates. This aided organizations that could not yet upgrade to the latest cumulative update. Note that applying the security patch and then upgrading to an older CU (rather than the latest) will expose your organization to the exploits again.
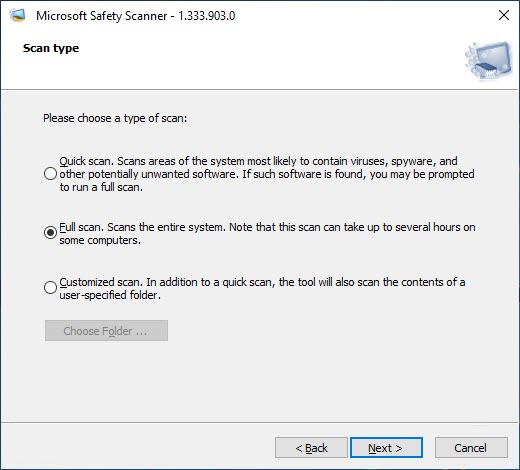
Once you are fully patched, I recommend running the Microsoft Safety Scanner (also known as the Microsoft Emergency Response Tool), which detects and remediates all known malware. This is a self-executing program that can be downloaded here.
I recommend running a full system scan. Note that it takes a few hours to run a scan, and it may spike your CPU, so it’s best to do this during a maintenance window. If you have a database availability group, consider putting the server into maintenance mode so that you can run the scanner with zero user impact.
The Safety Scanner will inform you of any malware detected, whether it was able to remove that malware, and any additional actions you may need to take (such as rebooting the server).
For a log of all detections and actions taken by the Safety Scanner, navigate to C:\Windows\Debug\msert.log. All scans performed by the Safety Scanner are logged in this file. In our screenshot below, the Safety Scanner reported no detectable threats.

As of March 18th, Windows Defender Antivirus can now detect and remediate known malware used in the March 2nd exploits.
To leverage Windows Defender Antivirus, click Start, search for Virus & Threat Protection, and select Virus & threat protection from the search list. From the Virus and Threat Protection window, select Scan Options, Full Scan, and click the Scan Now button.
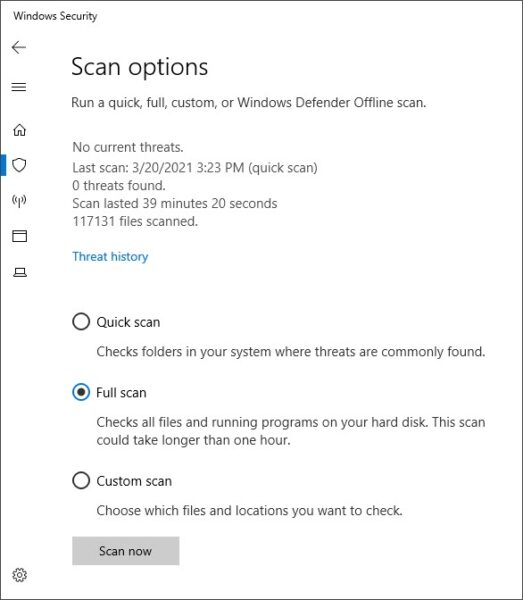
Running a full scan Windows Defender Antivirus may spike your CPU, so it’s best to do this during a maintenance window or scan each DAG member in maintenance mode. Windows Defender Antivirus will identify any threats and remediation taken.
For more depth and details, be sure to check out Microsoft’s full article: Guidance for responders: Investigating and remediating on-premises Exchange Server vulnerabilities – Microsoft Security Response Center. This article contains additional methods and scripts for detecting compromise. It also provides additional guidance on what to do if a threat is detected.
For breaking news and updates, be sure to follow the Microsoft Security Response Center: On-Premises Exchange Server Vulnerabilities Resource Center – updated March 18, 2021 – Microsoft Security Response Center.
So, what’s new in this Cumulative Update?
Aside from the security issues mentioned above, this cumulative update fixes several non-security issues reported by customers.
This update addresses:
- Users could not preview PDF files in Outlook on the Web. Instead, an attempt to view the file inline would trigger a download action.
- Microsoft Teams’ calendar tab may not display for on-premises mailboxes due to an Autodiscover V2 site awareness issue.
- Regional UPNs are overwritten when not present in the UPN suffix list.
- New health mailboxes created every time the Exchange Health Manager service is restarted
- Certain search scenarios returning unexpected results when Outlook is in online mode
- Unable to set the archive domain for a cloud-based archive.
- Updates to daylight savings
For a full list of all fixes, including security patches, be sure to check out the KBs KB4602570 and KB4602569.
The Exchange 2016 and 2019 cumulative updates will extend the schema. For more information on how to perform a schema update, check this article. For a full list of schema numbers, check this article.
If you run multiple versions of Exchange in coexistence, run SETUP /PrepareAD from the newest Exchange version. For example, if you have Exchange 2013 and Exchange 2019, run SETUP /PrepareAD from Exchange 2019.
Note: If you are running in a multi-domain environment, you will need to perform SETUP /PrepareDomain in each domain. You do not need to run /PrepareDomain in the domain where you performed /PrepareAD. /PrepareAD also invokes the /PrepareDomain process.
Need a refresher from Ignite 2020?
Unfortunately, Ignite 2021 did not give us much in the way of Exchange or Outlook news. If you need a refresher on all the Exchange features announced at Ignite 2020, I highly recommend checking out the article 15 Ignite sessions every Exchange admin should see (2020 edition). In this article, there are extensive notes on what each session contained. Also, those notes include timers if you need to jump to a specific topic.
Further Reading
Here are some articles I thought you might like.
- RunAs Radio #745 – Exchange Server vNext announced
- 15 Ignite sessions every Exchange admin should see (2020 Edition)
- Use Log Parser Studio in your Exchange & Office 365 migration planning
- RPC/HTTP & Block Legacy Auth may prevent Outlook reconfiguration after migrating to Exchange Online

So what do you think is coming next? What would you like to see? Drop a comment below or join the conversation on Twitter @SuperTekBoy.

Leave a Reply