Secure VPN Connection terminated by Peer.
Reason 433: Reason Not Specified by Peer
I ran into this error recently when trying to set up a Remote Access VPN. This error could be caused by multiple problems. However, in my particular case, it was the settings under AAA authentication servers. Upon connection, the VPN client would prompt for logon credentials and then immediately return this error.
In my environment, I was using a Windows Server 2003 Domain Controller for LDAP authentication. The VPN termination point was an older PIX 515 firewall running IOS 8.0. I was also using the latest Cisco VPN client on Windows 8.1.
After some quick troubleshooting, it appeared that the domain account used to query LDAP was either buried too deep in the OU structure or, some of the OU names were causing problems (they had spaces and special characters).
As a test, I moved the account back up to the root-level “Users” container. I then altered my DN settings on the firewall to reflect this change. The VPN client software connected immediately.
To be fair, I was configuring Remote Access VPN on a very old PIX 515. It could be that a newer ASA firewall running the latest IOS won’t have this particular issue. Either way, just something else to try if you get this error code.
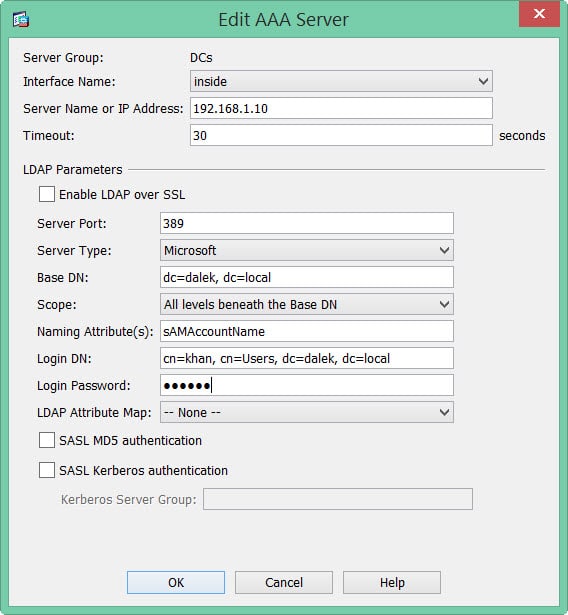
Lastly, here is a quick screenshot of a working AAA server configuration as well as an explanation of all the fields.
- Server Group: This is purely descriptive. Call it whatever you like.
- Interface Name: This is the name of the interface your AAA server can be located on. In my example, an interface called INSIDE.
- Server Name or IP Address: The name or IP address of your AAA server.
- Timeout: The default is 5 seconds. Set this to whatever makes you feel comfortable. I like 30 seconds.
- Enable LDAP over SSL: I typically leave this unchecked and do my LDAP queries over the standard 389 port. If you check this box it will default to port 636 and send queries over SSL.
- Server Port: The default LDAP port is 389. Most likely what you will have here.
- Server Type: For me, my LDAP server was Microsoft. You can pick other LDAP providers but the rest of these bullets will assume you are using Microsoft.
- Base DN: This sets wherein the hierarchy to start LDAP searches for users. We could drill this down to a specific OU. Or we could just use the root domain. For example dalek.local becomes dc=dalek, dc=local. (Being specific does have the potential to speed up LDAP queries!)
- Scope: I typically set this as All Levels Beneath the Base DN. This allows you to specify how deep from the Base DN you want LDAP queries to search.
- Naming Attributes: Specifies what to match against. In Windows, this is the account name, or, sAMAccountName.
- Login DN: The full path, including username, to the account used to perform the LDAP queries. In my case, the user was Khan and they were in the top level Users OU. Their domain is dalek.local. So, this becomes, cn=khan, cn=Users, dc=dalek, dc=local.
- All other options I leave as defaults.

Thanks for your post, helped me a lot
Grettigns from Mexico.