Why can’t I access my Cisco firewall through a web browser? There could be a number of reasons for this. We will explore the different causes in our multi-part series.
One possibility could be that you simply are missing the necessary configuration on your firewall. So let’s check this out.
First, we need to log in using an alternative method. Let’s use PuTTY to access the CLI (Command Line Interface).
PuTTY is an open source project and can be downloaded here.
http://www.chiark.greenend.org.uk/~sgtatham/putty/download.html
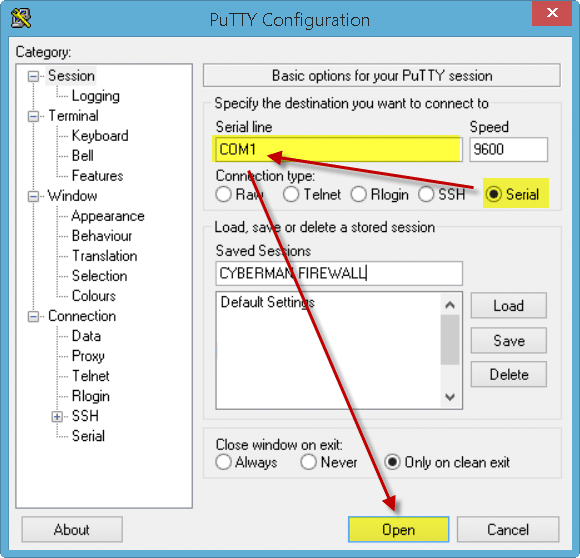
Once you have PuTTY double-click the executable. It will launch the window below.
In our example, we have Serial checked and will be connecting over COM1 at a speed of 9600 baud. We connect by plugging our computer into the Console Port on the Cisco with a management cable.
Alternatively, we could also select either Telnet or SSH and enter the IP address of the Cisco Firewall (assuming those have been configured).
When we hit the Open button we will be prompted to enter our credentials. Once entered we will be at a command prompt with a right corner bracket >.
firewall>
To make changes we need to log into privileged mode. To do this type ENABLE at the command prompt and hit enter.
We will be prompted for privileged credentials. Enter these and our command prompt will now end with a hash sign #.
firewall#
From here let’s make sure that our router is configured for ASDM. Type SHOW RUN HTTP. We should see an output similar to the following:
HTTP SERVER ENABLE
HTTP 192.168.1.0 255.255.255.0 inside
The first line enables ASDM (“web access”) on the firewall. The second line is an access list of what IP addresses can access the ASDM. In our example, anyone on the 192.168.1.0 subnet can access the ASDM from inside the network. If you don’t see an output like the above then we need to configure it.
CONFIGURE TERMINAL
This prepares the terminal session to receive commands.
HTTP SERVER ENABLE
HTTP <IP ADDRESS> <SUBNET MASK> <NAME OF INTERFACE>
In lieu of <IP Address> and <Subnet mask>, place the IP address of your own internal subnet. You could also lock this down to a single IP address, such as an administrator workstation or a server. For example:
HTTP 192.168.1.67 255.255.255.255 INSIDE
The subnet mask of all 255’s means that only that single IP address can connect to the ASDM service.
You could also open up ASDM from an external IP with a command like this.
HTTP 8.8.8.8 255.255.255.255 OUTSIDE
Personally, I don’t like opening up any more ports to the outside world than I need to so, use your best judgment here.
We are also assuming that your interfaces are named INSIDE and OUTSIDE. To check the name of your interfaces run the command:
SHOW RUN INTERFACE
This will return a list of all the interfaces on the firewall. Check for a line under each interface called NAMEIF. This is the name of the interface. For example, you may have a DMZ network connected to a physical interface that is listed as NAMEIF DMZ. Let’s say you want to open ASDM to the DMZ subnet. It may look something like this.
HTTP 10.0.0.0 255.255.255.0 DMZ
Once you have confirmed your subnet is allowed to access ASDM through the relevant interface and that the HTTP server is enabled, try reconnecting through your web browser.
If this works, be sure to save all your changes with the following command.
WRITE MEMORY
If the problem persists then we will explore additional causes in Part 2 of this series.
NEXT: Why can’t I access my Cisco firewall through a web browser? (Part II)

Leave a Reply