When attempting to use Connect-MsolService with an MFA-enabled admin account you may receive a legacy auth prompt as opposed to a modern auth prompt. This incorrect prompt is due to the MSOnline PowerShell module being out of date.
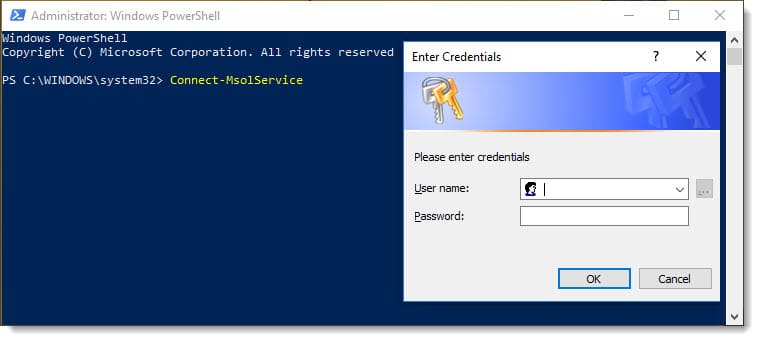
If you were to enter credentials in the legacy prompt you would be unable to connect and would receive the following cryptic error.
C:\> Connect-MsolService
Connect-MsolService : Exception of type 'Microsoft.Online.Administration.Automation.MicrosoftOnlineException' was thrown.
At line:1 char:1
Connect-MsolService
~~~~~~~~~~~~~~~~~~~
CategoryInfo : OperationStopped: (:) [Connect-MsolService], MicrosoftOnlineException
FullyQualifiedErrorId : 0x800434D4,Microsoft.Online.Administration.Automation.ConnectMsolService
So, all we need to do is update, right?
Well, depending on how you originally installed the MSOnline module the update process may not be intuitive as you might think.
Update the MSOnline PowerShell module
To determine what version of the MSOnline module you have installed on your machine, run the following:
C:\> Get-Module -Name MSOnline
ModuleType Version Name
---------- ------- ----
Manifest 1.0 MSOnline
In the example above you can see we have the original release of the MSOnline PowerShell module. To see what modules are available to download from the PowerShell gallery, run the following command.
C:\> Find-Module -Name MSOnline
Version Name Repository Description
------- ---- ---------- -----------
1.1.183.17 MSOnline PSGallery Microsoft Azure Active Directory Module
From this output, we can see version 1.1 is available.
Typically at this point, you would run the Install-Module command and get the latest version of the MSOnline module from the PowerShell Gallery. You would then be updated, and life would be good.
However, because version 1.0 was delivered as a standalone MSI we actually have to uninstall it first from Control Panel. If we don’t we will get all sorts of errors when trying to update, including recommendations by PowerShell to do a side-by-side or forced installation. All of which will error out anyway.
To remove version 1.0, navigate to Control Panel and Programs and Features. From the Uninstall or change a program dialog, select Windows Azure Active Directory Module for Windows PowerShell and click Uninstall. Click Yes to confirm.
Now let’s switch back to PowerShell and run the Install-Module command.
Note: You may be prompted to allow installation from an untrusted repository. With this being a known module from the PowerShell Gallery, type Yes and press enter. However, it is always wise to scrutinize all modules, regardless of where they are sourced.
C:\> Install-Module -Name MSOnline
Untrusted repository
You are installing the modules from an untrusted repository. If you trust this repository, change its InstallationPolicy value by running the Set-PSRepository cmdlet. Are you sure you want to install the modules from 'PSGallery'?
[Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "N"): Y
[PS] C:\>
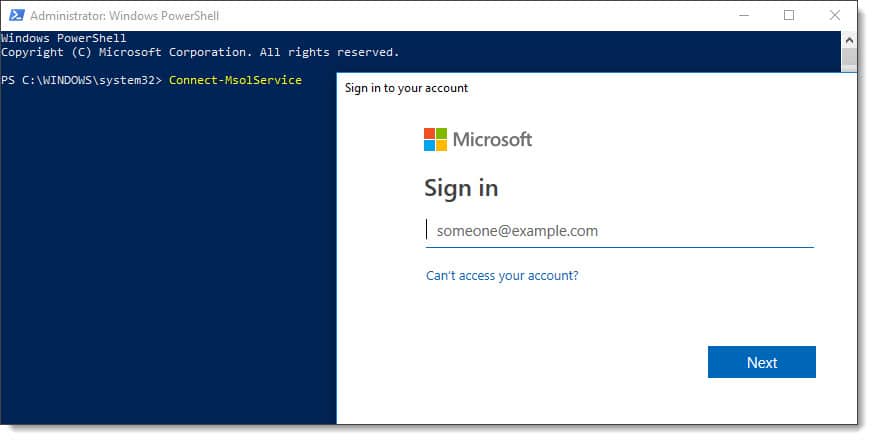
With the module updated you will need to close and reopen any PowerShell windows. With a new PowerShell window open, run the Connect-MsolService command. You should now be able to authenticate using MFA.

Have you run into this issue? What did you do to fix it? Drop a comment below or join the conversation on Twitter

Thank you! I looked at the terrible stuff Microsoft calls “documentation”, with absolutely no help. This was great information!
Too bad Microsoft can’t learn to put accurate information in their documentation like you have done here! I guess they need to learn their own product, since they seem to be clueless when it comes to things like this.
Very useful! Thank you!
Just a heads up my installation was listed differently from yours. It showed Microsoft Online Services Module for Windows Powershell instead of Windows Azure Active Directory.
See screenshot below:
https://i.imgur.com/UuZbSTi.png
Well done. Clear, concise and usefuly. Unlike anything Microsoft produce.
Thanks for that explanation mate, your blog post is far superior to any advice Microsoft gave me on technet.
it works!!
Thank you so much for this. It helped me to resolve my issue. I’ve been going back and forth with Microsoft trying to resolve this and got absolutely no where with them.
Thanks! That worked exactly as you wrote it.
Hello! I have a script which I used before the MSA and it didn’t required the credentials, is there a way to adapt this one to accept the infamous token?
Thank you and best regards.
Thanks Heaps for this Article. Worked for me