When trying to activate (or sign in to) Microsoft Office with your Office 365 enterprise credentials, you may receive the following error.
This feature has been disabled by your administrator.
This error is likely a result of a group policy.
To check this, open Group Policy Management Console (GPMC). From the GPMC, expand your domain name (e.g., skaro.local) and Group Policy Objects.
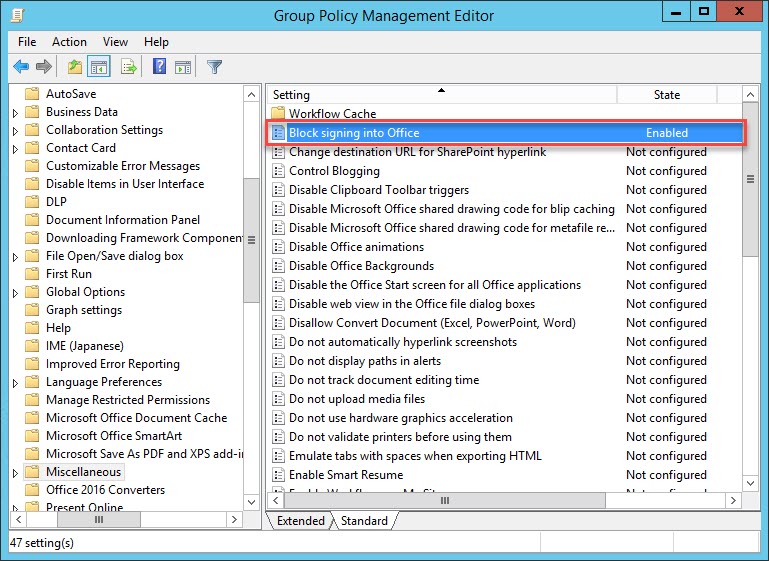
Select your policy that is managing the Office suite and click the Settings tab. Expand User Configuration (Enabled) > Policies > Administrative Templates > Microsoft Office 2016 > Miscellaneous. If you see a setting named Block signing into Office that is Enabled, this is the culprit.

Note: If you do not see this setting, I recommend checking all group policies currently applied to the impacted user. You can get this by running GPRESULT from a command prompt on your impacted user’s computer.
Resolving ‘This feature has been disabled by your administrator.’
To resolve this issue, right-click on the group policy in question and select Edit from the context menu.
From the Group Policy Management Editor expand User Configuration (Enabled) > Policies > Administrative Templates > Microsoft Office 2016 > Miscellaneous.
From the right-hand pane, double-click on Block signing into Office.
The Block signing into Office has four options. Which option you choose depends on the needs of your business. However, a selection of ‘None Allowed,’ which our example policy was set to, will block all Office activations and signing in, causing the error in the post title.
- Both IDs allowed permit both enterprise accounts (e.g., any account in your Office 365 tenant, whether a synced or cloud account) and Microsoft accounts (e.g., a personal account) to sign in to Office.
- Microsoft account only permits Microsoft accounts (e.g., a personal account). Enterprise accounts are blocked.
- Org ID only permits enterprise accounts (e.g., any account in your Office 365 tenant, whether a synced or cloud account). Microsoft accounts are blocked. This might be a great option to prevent users from connecting their personal accounts to the Office Suite on a corporate device. For example, this could block users from adding their personal OneDrive as target storage in the Office suite. Note that this does not block users from connecting their personal account to their OneDrive Sync client in Windows; it simply prevents them from adding their personal OneDrive directly to the Office suite.
- None allowed blocks any account from signing in to Office (or activating office).
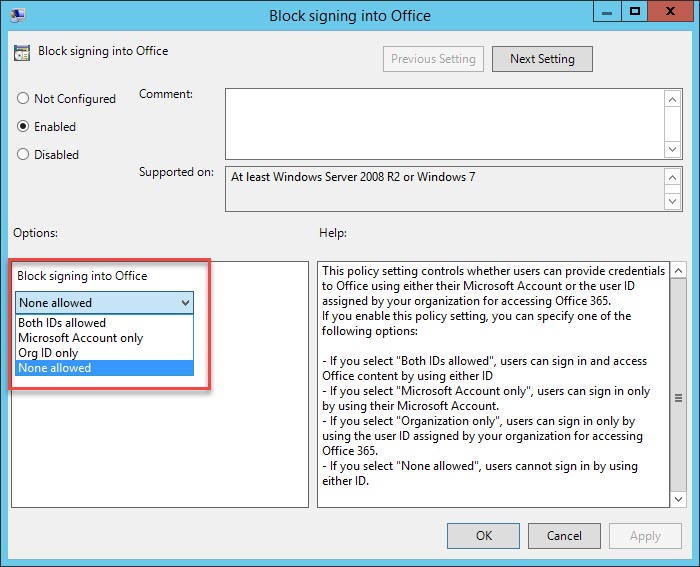
In our example policy, we will switch to Org ID only and click Ok.
You can either wait for the policy to propagate to workstations or force the policy to refresh immediately by running GPUPDATE /FORCE from a command line.

Have you seen this issue before? What did you do to fix it? Drop a comment below or join the conversation on Twitter @SuperTekBoy

Leave a Reply