In May, Microsoft released a cumulative update for Exchange 2019. Once you get the H1 2023 cumulative update, be sure to grab the security updates released in June.
While Exchange 2016 did not receive a cumulative update, it did get a June security update, so be sure to install it.
Exchange 2013 did not get any updates as it is officially out of support. If you are on Exchange 2013, you should upgrade to Exchange 2019 or migrate to Exchange Online. No future security updates are planned for Exchange 2013.
If you need guidance on migrating from a specific CU to the latest, check out Microsoft’s Exchange Update Wizard for step-by-step instructions.
The updates are as follows:

Exchange 2019:
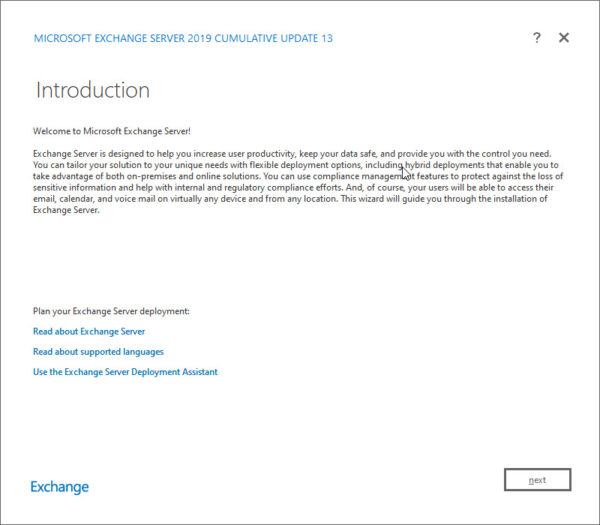
Cumulative Update 13 (KB5020999) | June 2023 Security Update (for CU13)

Exchange 2016:
No new cumulative update | June 2023 Security Update (for CU23)
Exchange 2013 is out of extended support
Exchange 2013 exited extended support on April 11th, 2023. This means that there are no more security patches or technical support for these products. Any security patches after April 11th, 2023, are at Microsoft’s discretion. At the time of writing, the last update for Exchange 2013, is the March 14th, 2023 security update.
Due to the lack of security patches, it is imperative to upgrade these products to either Exchange 2019 or Exchange Online as soon as possible. For more information on how to migrate to Exchange 2019 or Exchange Online, check out Microsoft’s deployment guides here.
Modern Authentication
Cumulative Update 13 adds native OAuth2.0 support to Exchange 2019. Previously if you wanted to leverage modern authentication with Exchange 2019, you had to establish hybrid connectivity with Exchange Online and implement Hybrid Modern Authentication.
This update removes that requirement allowing you to implement modern auth with entirely on-premises technologies. To implement native modern auth in Exchange 2019, you will need to meet the following requirements:
- Exchange 2019 CU13 or later
- Active Directory Federation Services 2019 (ADFS 2019) or later
- Outlook for Windows (Version 2304 – Build 16327.20214) running on Windows 11 (Version 22H2 with KB5023706 installed)
- Outlook on the Web
Note: Modern auth support for Outlook for Mac, Outlook Mobile, and native mail apps will be added in a later update. At the time of writing, these clients will continue to use basic auth to connect to Exchange 2019.
Enabling modern auth, either through native modern authentication or hybrid modern authentication, greatly increases the security posture of Exchange on-premises. With native modern auth, organizations leveraging Exchange on-prem can utilize ADFS as their identity provider. This allows for multi-factor authentication, smart card authentication, certificate-based authentication, and integration with third-party authentication providers.
For more information on deploying native modern authentication for Exchange 2019, check this article.
Configuration Backup and Restore
One of the common pain points with cumulative updates was that it could wipe out any customizations you may have made to web.config or sharedweb.config files. One common customization was integrating Skype chat into Outlook Web Access via config files. To combat this, administrators would need to back up and then later restore any customizations after a cumulative update was applied.
Starting with cumulative update 13, the install process now preserves 71 different configuration settings across multiple config files. For a full list of the 71 customizations that are preserved during the update process, check this article. If your customization is not included in this list, you will still need to backup and restore your customization after each update.
Hybrid Configuration Wizard switches to REST API
With the deprecation of Exchange Online Remote PowerShell (RPS), the Hybrid Configuration Wizard has been updated to leverage the new REST APIs (the same APIs used by the Exchange Online PowerShell Module v3).
The wizard itself will look exactly the same, but the underlying technology will leverage REST-based PowerShell cmdlets. The old wizard will fail to connect, so be sure to get the latest wizard from https://aka.ms/hybridwizard.
For more information on the updated Hybrid Configuration Wizard, check this article.
Updates on the Exchange Server Antivirus Exclusions
It is important that file-level antivirus scanners installed on Exchange have the necessary exclusions in place. This ensures that files (such as the mailbox database) or processes that handle these files (such as the information store) are not locked by a scanning or quarantine process. Microsoft publishes an exhaustive list of all exclusions here.
However, Microsoft has recently removed the need to have a handful of these exclusions. The following exclusions can be removed and reintroduced into your scanning process.
Folder exclusions that can be removed:
%SystemRoot%\Microsoft.NET\Framework64\v4.0.30319\Temporary ASP.NET Files
%SystemRoot%\System32\Inetsrv
Process exclusions that can be removed:
%SystemRoot%\System32\WindowsPowerShell\v1.0\PowerShell.exe %SystemRoot%\System32\inetsrv\w3wp.exe
For more information, check Microsoft’s article here.
Transport Enforcement System
Microsoft announced a plan to start throttling and blocking unsupported and non-compliant versions of Exchange Server that use the connector type of “on-premises” to send email to Exchange Online.
- Unsupported versions of Exchange, which at the time of writing are Exchange 2007, Exchange 2010, and Exchange 2013, will be initially throttled and then later blocked from sending mail to Exchange Online.
- Supported versions of Exchange, which at the time of writing are Exchange 2016 and Exchange 2019, must remain up to date on cumulative and security updates to remain compliant. Non-compliant versions of Exchange 2016 and Exchange 2019 will be throttled after 30 days and blocked after 90 days of non-compliance.
The key takeaway is that if you send mail from Exchange on-premises servers to Exchange Online, you must upgrade or patch Exchange Server to a supported version. For more information, check https://aka.ms/BlockUnsafeExchange.
Installation tips
If you are current on your Exchange updates, these cumulative updates will not extend the schema. You will, however, need to run /PrepareAllDomains after installing this cumulative update.
Setup.exe /IAcceptExchangeServerLicenseTerms_DiagnosticDataON /PrepareAllDomains
or
Setup.exe /IAcceptExchangeServerLicenseTerms_DiagnosticDataOFF /PrepareAllDomains
If you are running Exchange 2016 CU20 or earlier or Exchange 2019 CU9 or earlier, you will need to perform a schema update. For a complete list of schema numbers, check this article.
The security updates (SUs) are now available as self-extracting executables, which means they will automatically elevate with administrative rights. However, the MSP delivery method requires admins to manually instruct the update to run with administrative rights. If admins missed this step, the security update could apply incorrectly, causing an outage in Exchange. The MSP delivery method is still available via the Microsoft update catalog, should admins prefer it. However, the EXE delivery method is better for admins wanting to install the security update manually. Note that this does not change the delivery method for cumulative updates–that remains the same.
Bug Bounty for Exchange Server
Following the HAFNIUM exploits in 2021, Microsoft added a bug bounty program for Exchange Server. Individuals can receive monetary rewards for submitting security vulnerabilities found on a supported version of Exchange Server running on the latest fully patched version of Windows.
Need a refresher from Microsoft Exchange Conference 2022?
If you need a refresher on all the Exchange features announced at Microsoft Exchange Conference (MEC) 2022, I highly recommend checking out the article, 8 MEC sessions every Exchange admin should see (2022 Edition). In this article, there are extensive notes on what each session contained. Also, those notes include timers if you need to jump to a specific topic.
Further Reading
Here are some articles I thought you might like.
- 8 MEC sessions every Exchange admin should see (2022 Edition)
- RunAs Radio #880 – Dealing with Vulnerable Exchange Servers
- Renew a Certificate in Exchange 2016 & 2019
- Office 365 for IT Pros (2024 Edition) released

So what do you think is coming next? What would you like to see? Drop a comment below or join the conversation on Twitter @SuperTekBoy.

Leave a Reply