One of the new Exchange Admin Center benefits is that many of the global mail flow settings that were previously only available via PowerShell are now available in this new GUI. For example, the Mail Flow settings page allows you to define several global transport configurations. This article will look at these settings and what they do. These settings are:
- Plus addressing
- Sending from aliases
- Enabling SMTP AUTH protocol
- Legacy SMTP AUTH endpoint for TLS 1.0 / TLS 1.1 clients
- Reply-All storm protection
To find these settings, log into the new Exchange Admin Center and navigate to the Settings tab on the left navigation pane. Then select Mail Flow.

This will pop out a dialog with the following options.

Plus Addressing
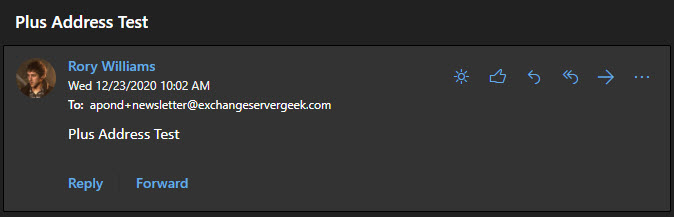
Plus addressing allows users to create their own unique email addresses by leveraging a plus sign in their email address—for example, apond+newsletter@exchangeservergeek.com. Anything after the plus sign is completely at the discretion of the user.
This becomes particularly useful when you want to target newsletters to a unique email address, especially when configuring inbox rules. It is also helpful to determine who might have sold or leaked your email address.
To enable this feature from the new Exchange Admin Center, navigate to Settings > Mail Flow. From the pop-up window, select Turn on plus addressing from your organization and click the Save button.
If you prefer to enable this from PowerShell, log onto Exchange Online PowerShell and run the following command.
C:\> Set-OrganizationConfig -AllowPlusAddressInRecipients $true
To confirm the setting has taken effect, run Get-OrganizationConfig.
C:\> Get-OrganizationConfig | FL AllowPlusAddressInRecipients AllowPlusAddressInRecipients : True
Users can then start leveraging plus addresses. Emails addressed to a plus address will appear in the user’s inbox without any further user intervention. From there, the user can build inbox rules for the plus addresses if they desire.
Reference: Plus Addressing Now Available in Exchange Online
[Read more…] about Configure global mail flow settings from the new Exchange Admin Center