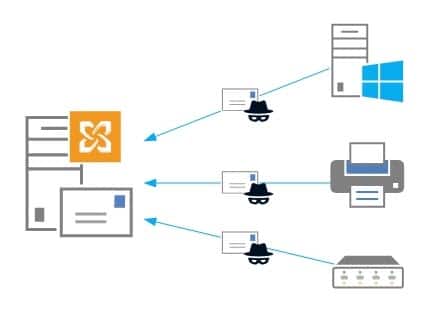
Group Writeback is a feature in Azure AD Connect that allows for Office 365 Groups to be written back to your on-premises Active Directory as a universal distribution group. This allows your on-premises users in a hybrid environment to send email to the Office 365 Group.
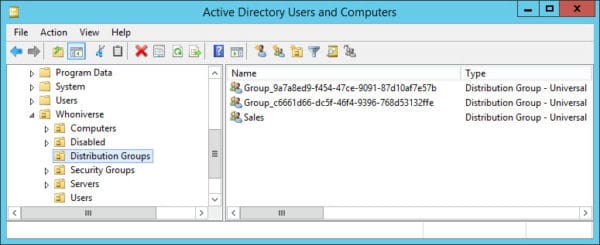
When configuring group writeback you specify which organizational unit (OU) you want these objects to be written. Each of these Office 365 groups is then represented by a separate universal distribution group that starts with the name of “Group_” followed by a unique identifier.
In the screenshot below I have two Office 365 groups that are being written back to my local AD.
The problem – Access is Denied
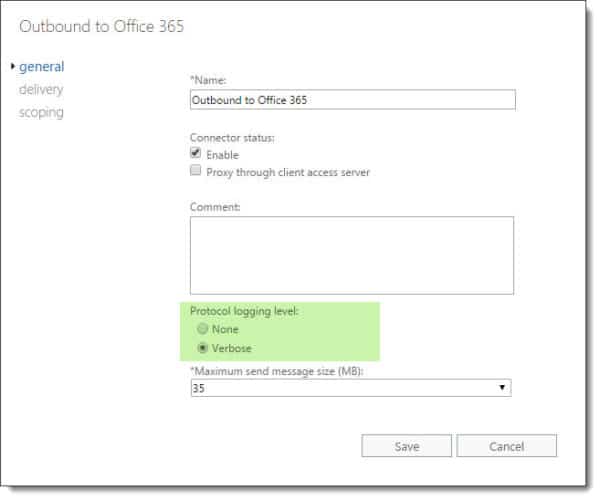
When I first tried to get these groups written back to this organizational unit was where I ran into problems. I was following this Microsoft document verbatim. The document specifies to open Active Directory Users and Computers and locate the account that started with “AAD_”. Which I found.
The document later uses this account to run a script. When running the script everything completed as expected. No errors.
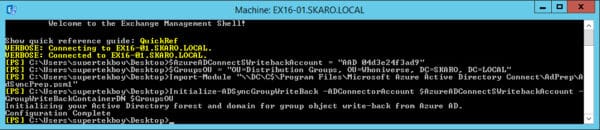
When I checked the permissions on the organizational unit I could see that the script had added the AAD_ account with a bunch of permissions. Everything looked good.
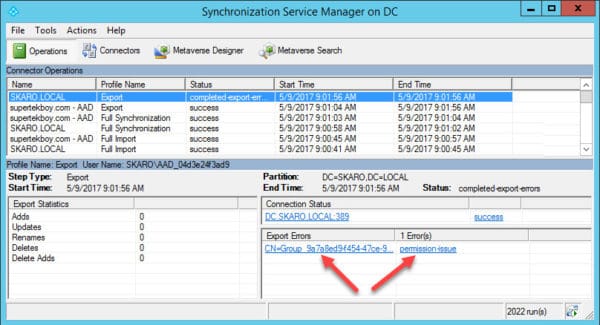
However, I quickly started generating errors in Azure AD Connect. When I opened the Synchronization Manager I received the following error on the export of my Office 365 group. “Permission Issue – Access is denied”