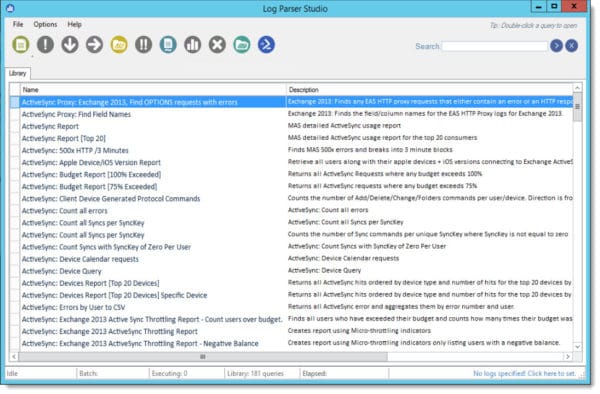
One of the great unsung heroes is Log Parser Studio. This utility allows you to easily parse through gigabytes upon gigabytes of IIS logs to find the information you need. Without this tool, this task is tedious in a single Exchange server environment and orders of magnitude worse in Exchange environments with many servers.
Log Parser Studio is great when it comes to migration planning and discovery, and it is a tool I always have in my tool belt. It does not matter if you are migrating to a newer version of Exchange or Office 365; Log Parser Studio can aid in the planning for both scenarios. For discovery, I use it in the following two ways:
- First is to identify third-party integrations, such as those from a voicemail system, fax solution, or conference room system
- Second is to identify all client software connecting to Exchange
Once you have identified the third-party integrations and clients, you can add them to your migration plan and determine the next steps. This could include upgrading legacy Office clients or testing the integration of a third-party app against the target system.
Discovery with Log Parser Studio becomes especially useful in environments where Exchange predates the current IT team or where knowledge and documentation have been lost over time.
In this article, we will explore how to use Log Parser Studio to identify the multitude of client software and third-party integrations.
Let’s get started!
Installing Log Parser Studio
Log Parser Studio comes in two downloads. The first is the original command-line utility known as Log Parser. The second is Log Parser Studio which was later developed to give a GUI to that command-line. We will need to download both components for this process.
Tip: I recommend installing Log Parser on a workstation and not directly on an Exchange server. That way we avoid adding unnecessary CPU cycles to the Exchange server.
First, we need to install Log Parser 2.2. Double-click on the LogParser.msi. On the installation screen, click Next. Accept the license agreement and click Next. On the Choose Setup Type screen, click Complete. Click Install. After the installation completes, click Finish.
Next, we need to install Log Parser Studio. Unzip the file LPSV2.D2.zip (I recommend unzipping this to your desktop). Open the newly created LPSV2.D2 folder and launch LPS.EXE.

This will launch Log Parser Studio.