Deprecation of the classic Exchange Admin Center
The new Exchange Admin Center has been available for quite some time and was designated reaching general availability back in April. With feature parity met, and in many cases exceeded, it is no doubt that the Exchange team is now planning the deprecation of the classic Exchange Admin Center.
Starting this month features will be redirected away from the classic admin center with the planned removal of the classic EAC by September 2022. Check out Microsoft’s timeline in the image below.

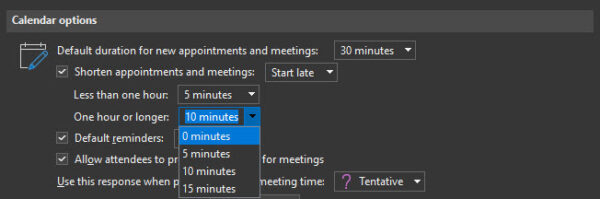
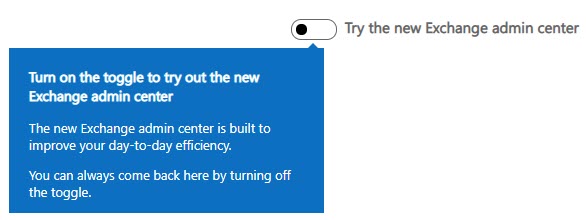
To use the new Exchange Admin Center point your browser to https://admin.exchange.microsoft.com or from the classic Exchange Admin Center select the toggle to Try the new Exchange Admin Center in the top-right of the screen.
New end date for Basic Authentication
Since 2018 Microsoft has announced the blocking of basic authentication. However, due to the pandemic, that date has shifted a few times. Back in February, it was announced that the deprecation of basic auth had been put on hold until further notice. In September Microsoft announced new deadlines for the deprecation of basic authentication for all Exchange protocols. This date is October 1st, 2022. After this date, any application connecting to Exchange Online will be required to leverage modern authentication (OAuth 2.0). The only exception to this is SMTP Auth which can continue to use basic authentication.
Note: Prior to October 1st, 2022, Microsoft will continue to disable basic auth on protocols in tenants where basic auth is not detected.
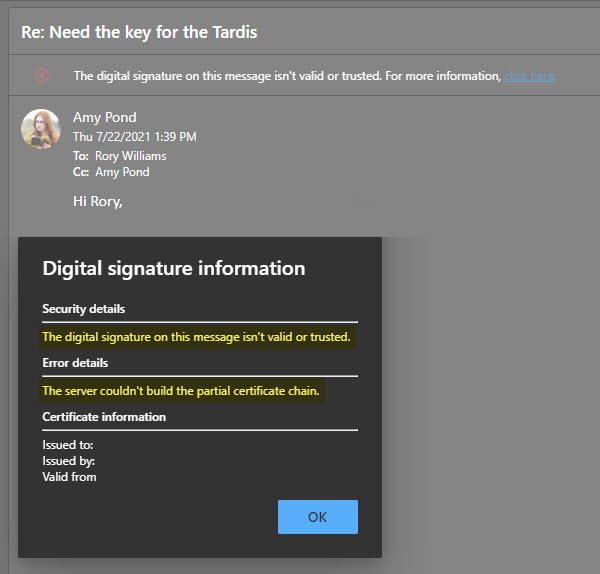
For devices and applications that integrate with Exchange Web Services, such as voicemail, ticketing systems, or line of business applications, these will be required to support modern authentication. One option is to leverage certificate-based authentication leveraging an Azure app. However, it is better to switch the EWS integration over to Microsoft Graph as Microsoft plans to deprecate EWS integration starting September 30th, 2022. Microsoft is positioning Microsoft Graph to be the sole entry point for all app integrations rather than having separate entry points for each Office 365 workload. This reduces the attack footprint of the Office 365 service. I would also recommend looking into Application Access Policies. These policies limit what mailboxes an app can access. Be sure to check your vendor’s documentation for guidance on connecting these apps to Office 365 with modern authentication.
For PowerShell, I recommend using the Microsoft Exchange Online PowerShell Module. This module supports both modern auth and is a requirement if your admin account has multi-factor authentication enabled (which I hope it does!). I recommend checking out this article for more information on how to use this module. Also, you may want to look into the Azure Cloud Shell. Check out the tutorial; Using Exchange Cmdlets in Azure Cloud Shell.
For POP and IMAP, Microsoft added OAuth support. However, this still requires your POP or IMAP application to support OAuth. For integrated apps that use POP or IMAP, like helpdesk ticketing systems, I would recommend looking for other methods of integration rather than using POP or IMAP. Using our helpdesk ticketing system example, look to see if the app can integrate with EWS or the Graph instead. For clients, see if you can switch those users over to a new client that supports a direct Exchange connection. My recommendation is to get rid of POP and IMAP entirely and globally shut down those legacy protocols.
The most significant impact of this announcement will be on ActiveSync. Countless native mail apps use ActiveSync to access their Office 365 mail. I highly recommend migrating your user base to Outlook mobile (for iOS and Android). Outlook Mobile supports both modern authentication and multi-factor authentication. It is worth noting that some native mail apps, such as those included in iOS 11+, have modern authentication support. However, pushing users to Outlook Mobile versus upgrading their phones is the path of least resistance. Not to mention your helpdesk or IT department will only need to support one mail client and have greater control protecting corporate data via mobile application management policies from Intune.
To track which devices and applications are signing in with legacy authentication, you can use the Azure AD Sign-ins dashboard. Microsoft covers this process in this article.
[Read more…] about Exchange Online Updates (October 2021)