The PowerShell command to recover deleted email for a user has been around for some time. However, these PowerShell commands now have a graphical interface in the new Exchange Admin Center.
In this article, we explore how to recover deleted email for a user. But first, there are some permission prerequisites.
Assigning your admin account recovery permissions
Before we can restore mail for a user we need permission to do so. The permission in question is the Mailbox Import / Export permission. By default, no one is assigned this permission in Exchange.
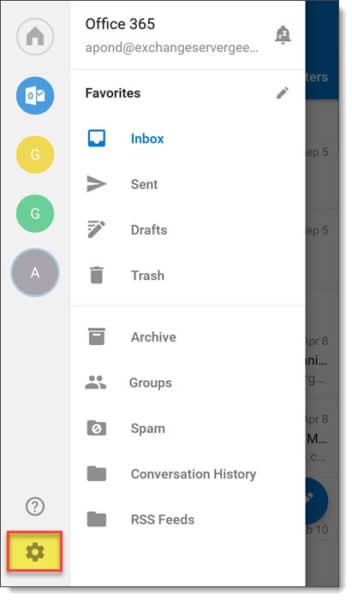
Log onto the Exchange Admin Center and navigate to Permissions > Admin Roles.
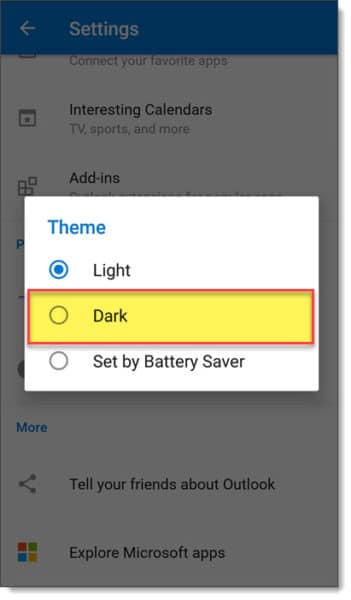
At this point, we have two options. We can either assign the Mailbox Import / Export role to an existing role group (such as Organization Management) or, we can create a new role group. Let’s do the latter.
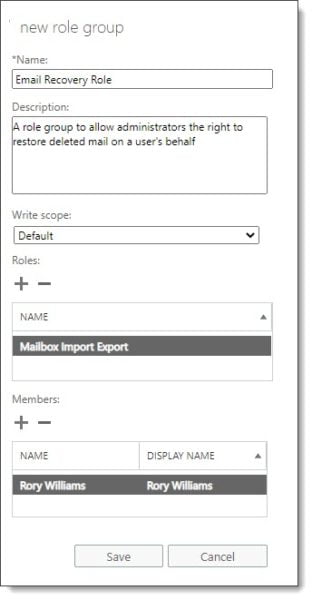
Click the New button ( ). This launches the new role group dialog.
). This launches the new role group dialog.
Type a Name and Description for your role. In our example, we went with Email Recovery Role.
If needed select a custom write scope, or, leave at default. The default scope allows the role holder to apply these permissions to the entire organization. You can define a custom write scope to limit the scope of this permission. For example, the scope could be limited to a specific business unit or group of users. This is particularly useful if you need to delegate this role.
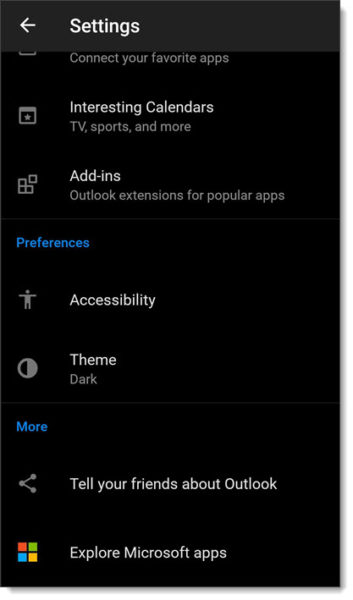
Under Roles click the Add button ( ).
).
Double-click Mailbox Import Export and click Ok.
Under Members click the Add button ( ).
).
Double-click each administrator you want to assign this role and click Ok.
Click Save.
Note: Once the role group is created it can take up to one hour for the permissions to take effect.
[Read more…] about Recover deleted email using the new Exchange Admin Center